CosaNostra v1.2 HTTP BotNet | Educational Analysis of BotNet Features
https://telegra.ph/cb-01-24-2
CosaNostra v1.2 HTTP BotNet is a sophisticated software tool designed for automating and managing remote systems. In this educational overview, we analyze its components, workflow, and potential use cases for security research and learning purposes. This examination highlights the importance of understanding network monitoring, remote administration, and cybersecurity ethics.
🔹 Core Functionalities:
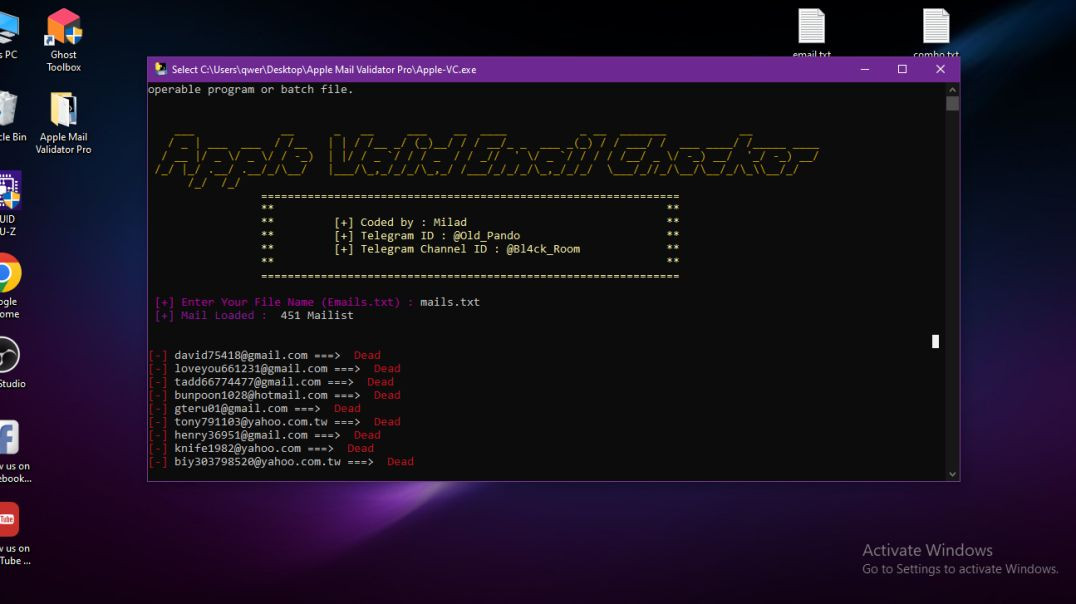
Keylogger: Monitors keystrokes for analysis in controlled environments
Clipper: Protects or extracts data from specific applications
Screenshot Capture: Provides visual monitoring for educational research
File Stealer: Can access and download files such as documents, photos, and text (for safe sandbox testing)
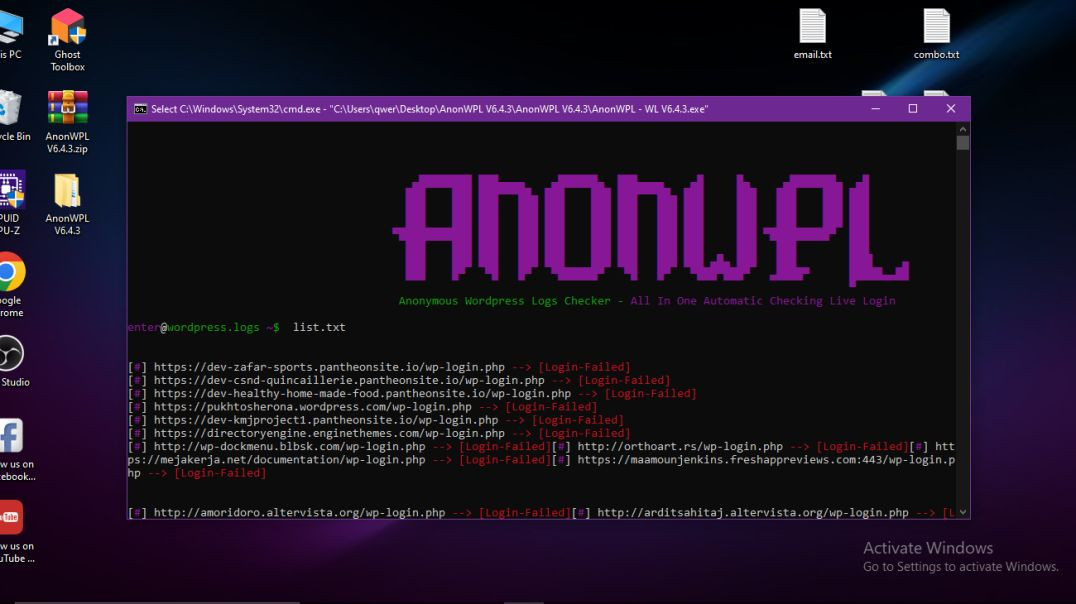
Download & Execute (Loader): Executes remote scripts in isolated testing environments
Device Information Collection: Retrieves system info like PC Name, OS, Firewall status, RAM, Antivirus, and Processor
Geolocation & Address Identification (educational simulation)
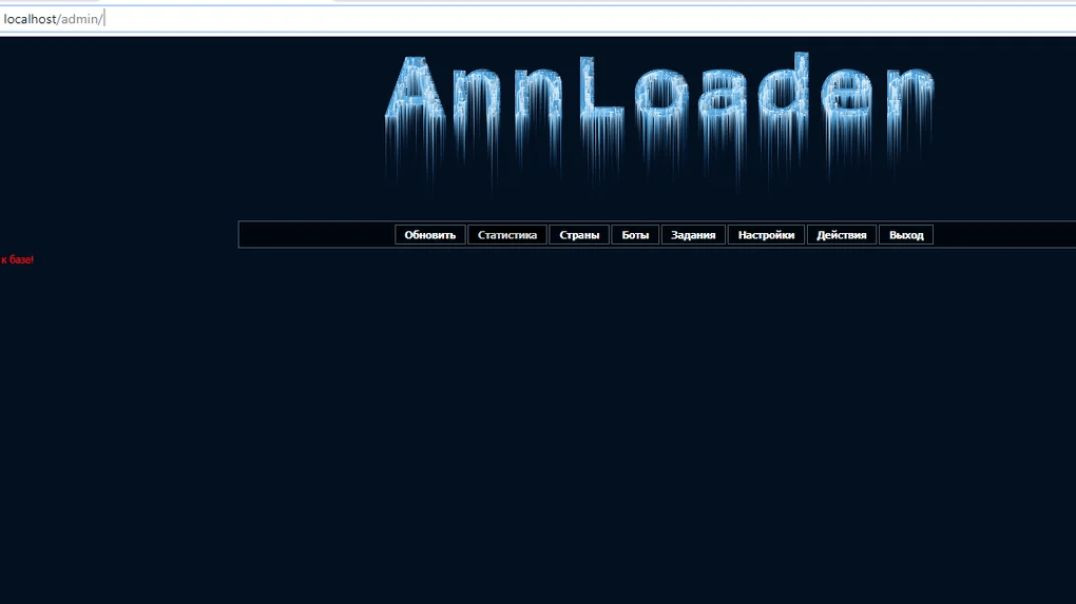
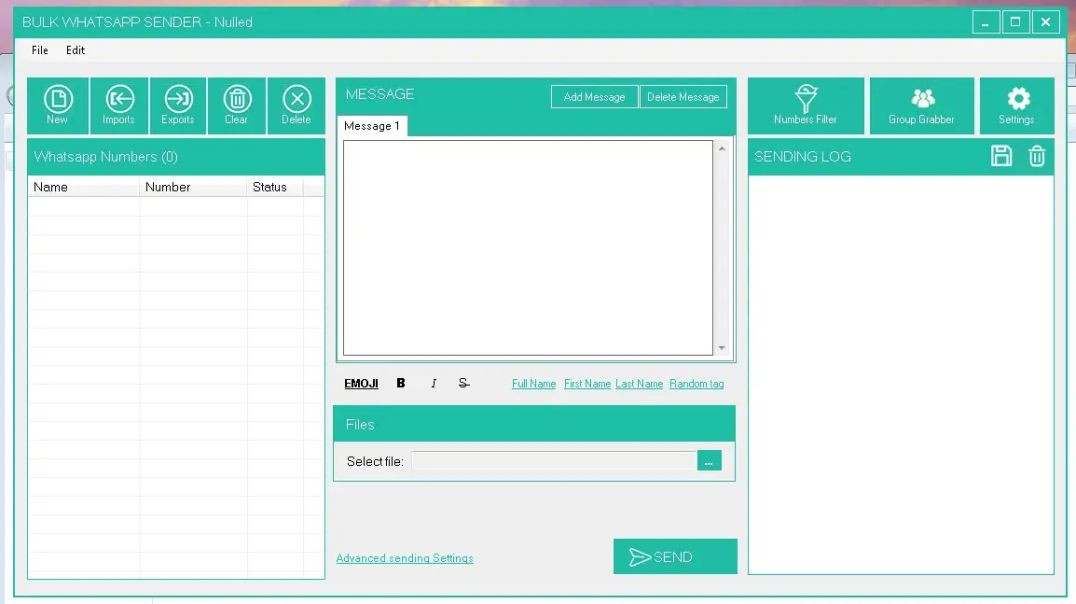
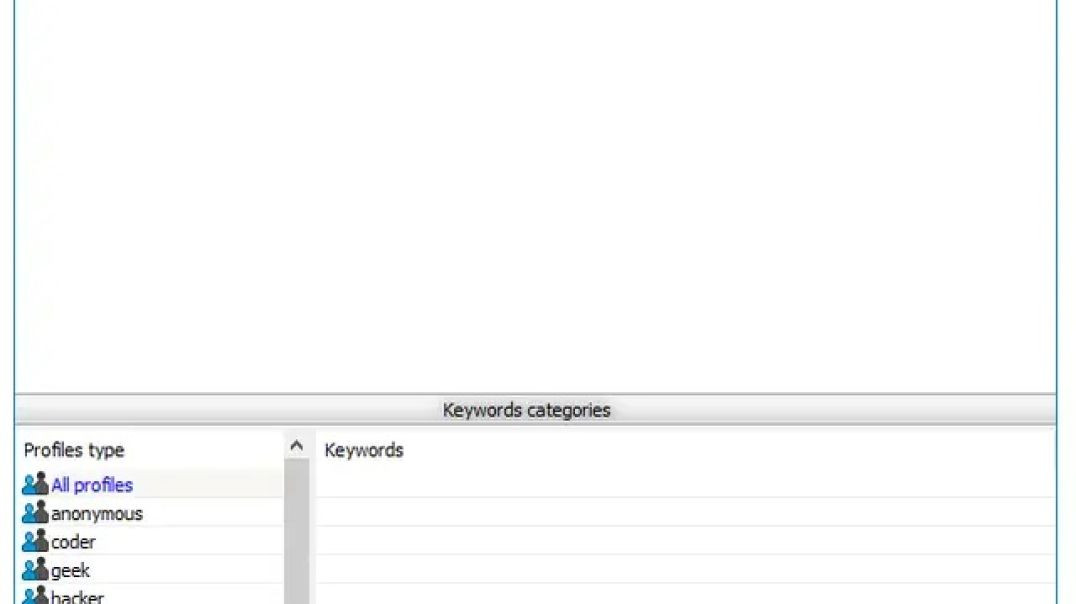
🔹 Interface and Management:
Dynamic and responsive web pages suitable for desktops and mobile devices
Home page displays bots, counters, keylogger reports, screenshots, HWID, IP, status, and last seen
Settings page for scheduling and managing tasks securely in sandboxed labs
Tasks page allows addition or removal of download/execute jobs in controlled environments
User page for updating information or managing accounts during testing
🔹 Educational Perspective:
Studying CosaNostra allows students and cybersecurity researchers to understand botnet operations, remote administration techniques, and defensive strategies. By analyzing its functions in isolated environments, learners can gain insights into malware behavior, network security, and ethical use of advanced software tools.
🔹 Ethical Considerations:
Use of tools like CosaNostra outside controlled labs or without explicit consent is illegal. Educational simulations should always be done in sandboxed environments, virtual machines, or isolated networks to prevent harm. Understanding botnet functionality enhances cybersecurity defense knowledge and responsible technology use.









لم يتم العثور على تعليقات